Release Notes
Security Announcement
Announcements
api.example.com trusts a specific IP range to access test devices and internal services. The trusted IP range is 123.123.123.0/24 . For access requests from the trusted IP range, no scanning related to the Web protection feature is performed to avoid false blocking. The steps are as follows:api.example.com, to enter the configuration page for the security policy of the target domain name.api.example.com and Client IP equal to 123.123.123.0/24 . Select the action as all options in the specified security module, including Managed rules , rate limiting , custom rules , Adaptive Frequency Control, Client Filtering, Slow Attack Defense and Bandwidth Abuse Protection , and Bot management .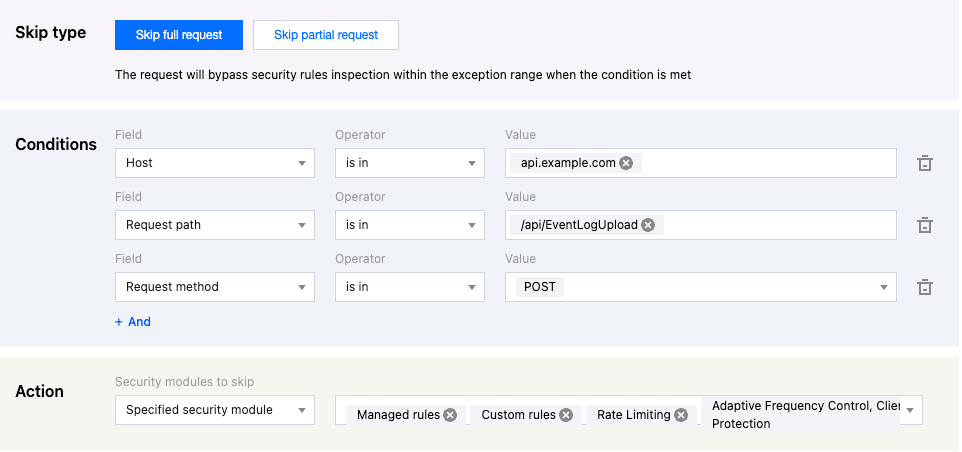
123.123.123.0/24 are not blocked by the security features of the Web protection module. This method avoids false blocking of the testing and internal service requests.api.example.com, and the API interface for event reporting is /api/EventLogUpload. In the event of a business surge, there may be a burst of high-frequency access scenarios. Such access patterns are highly likely to be identified as attacks by CC attack defense and intercepted. For this interface, you can configure exception rules to skip the CC attack defense module to avoid false interception. The operation steps are as follows:api.example.com, to enter the configuration page for the security policy of the target domain name.api.example.com , Request method (Method) equal to POST , and Request path (Path) equal to /api/EventLogUpload . Select the exception rule range as Adaptive Frequency Control, Client Filtering, Slow Attack Defense and Bandwidth Abuse Protection in the specified security module. You can configure multiple matching fields, and there is an AND relationship between the matching fields. For details of the matching conditions, see Match Conditions.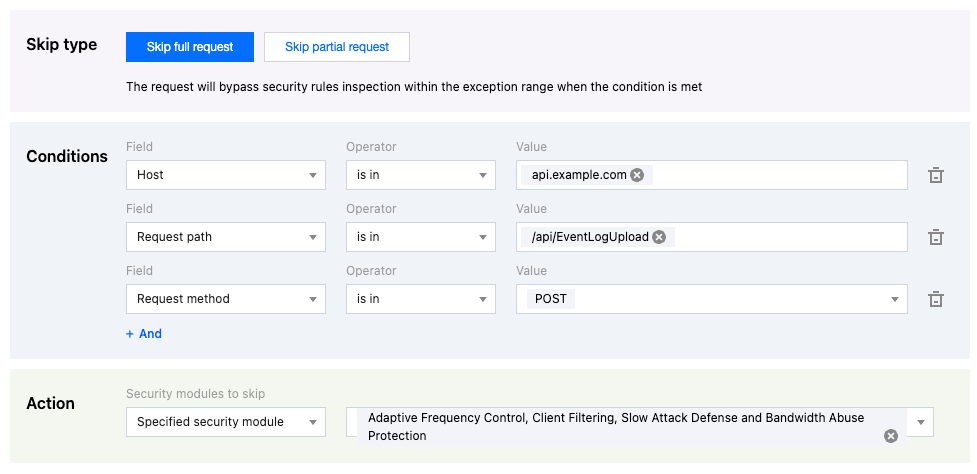
POST requests from the API for reporting the event logs are not blocked by feature modules such as Adaptive Frequency Control. This method avoids false blocking due to high-frequency log reporting, and meanwhile enables normal detection and protection for other APIs.blog.example.com, which is used for blog content sharing. The blog is based on WordPress. The blog content may share technical content related text (such as: SQL and Shell command examples), and when publishing the blog, the blog content text may trigger the attack defense rule due to matching SQL injection attack features. Through exception rules, you can configure request parameter allowlist, match the blog publishing API interface path /wp/v2/posts, and specify that the text parameter Content in the publishing content request does not participate in SQL injection attack rule scanning, avoiding false alarms and interception of blog content. The operation steps are as follows:blog.example.com, to enter configuration page for the security policy of the target domain name .blog.example.com and Request path equal to /wp/v2/posts . Select the exception rule range as Specified managed rules, including all SQL injection attack protection rules. Configure no scanning for the parameter content with the parameter name equal to content and the parameter value matching the wildcard * in JSON requests. For details of the matching conditions, see Match Conditions.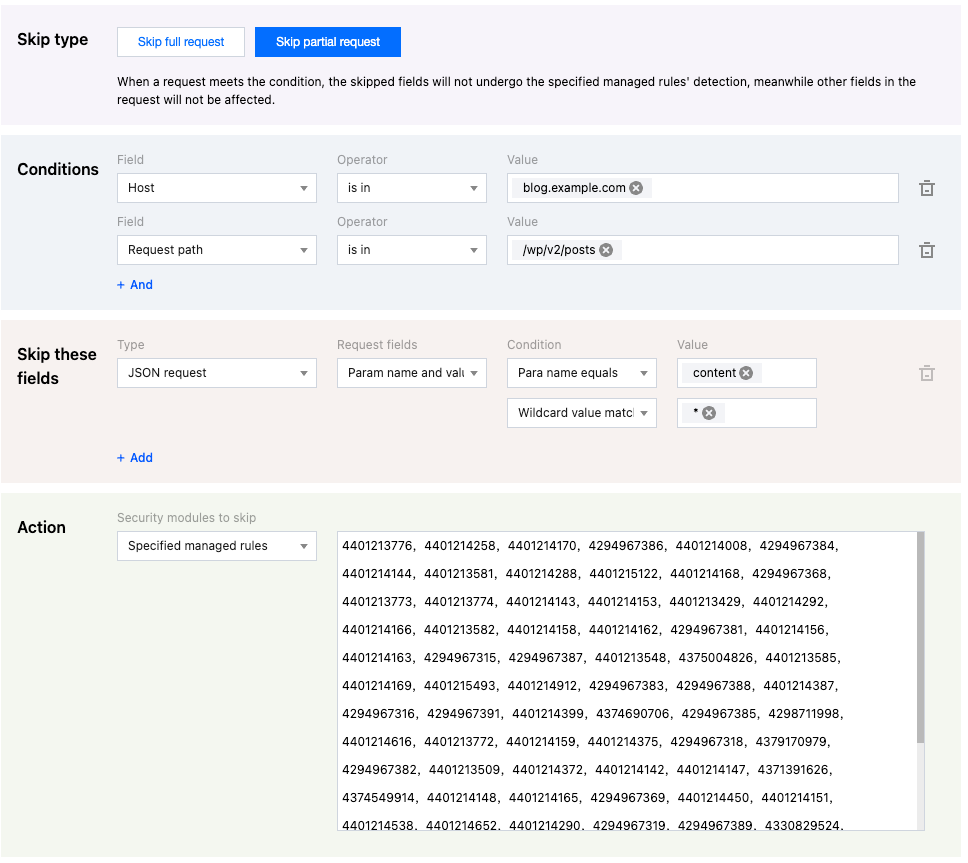
/wp/v2/posts request path, the blog content is not verified by the SQL injection attack protection rules. This method prevents normal text content from being wrongly identified as an attack through scanning.Category | Option |
JSON Request Content | All parameters Match specified parameter name Match condition parameter |
Cookie Header | All parameters Match specified parameter name Match condition parameter |
HTTP Header Parameters | All parameters Match specified parameter name Match condition parameter |
URL Encoded Content or Query Parameters | All parameters Match specified parameter name Match condition parameter |
Request Path URI | Query parameter part Partial path Complete path |
Request Body Content | Complete request body Segmented file name |
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback