异常登录的消息提醒
Download
聚焦模式
字号
现象描述
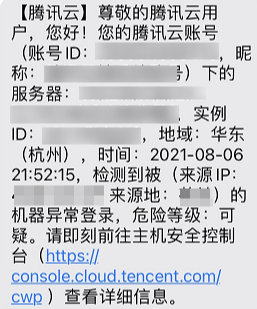
用户接收到腾讯云发送的服务器被异常登录的消息提醒,如下以短信消息为例:
可能原因
当您腾讯云账号下的服务器有登录行为时,腾讯云主机安全若发现本次登录没有命中登录白名单,会根据智能算法将该登录记录标记为“可疑”或“高危”,并触发实时告警提醒。
处理步骤
在收到的异常登录告警提醒后,请您按照下列步骤进行确认:
1. 请确认本次登录行为是否为合法登录。
是,请将该登录记录加入白名单,后续该登录行为再次发生,不再产生告警。

否,请执行步骤2。
2. 确定为非法登录,初步判断您服务器告警的异常登录事件,是由于不常使用的用户被破解,建议您立即修改登录密码以及服务器上保存过的相关登录凭证。建议参考 Linux 入侵类问题排查思路 和 Windows 入侵类问题排查思路对服务器进行常规排查。
加固方法
后续您可以通过如下加固方法,以提高服务器安全性:
服务器设置大写、小写、特殊字符、数字组成的12-16位的复杂密码。
修改云服务器 Linux 系统默认远程登录端口,如下所示:
修改文件:/etc/ssh/sshd_config
Port 22 #在第三行或第四行,如果前面有井号,请删除,修改为65534以下即可
可在远程连接中用 vi 命令,或 sftp 下载到本地修改,修改后使用以下命令重启 ssh 服务。
/etc/init.d/sshd restart #centos系统,重启ssh服务命令/etc/init.d/ssh restart #debian/ubuntu系统,重启 ssh 服务命令
腾讯云平台有安全组功能,建议您仅放行需要的业务协议和端口,不建议放行所有协议所有端口 ,详情请参考 创建安全组。
配置云服务器系统防火墙,建议开启 云防火墙 并设置互联网边界规则。
确保云服务器已安装的防护软件 主机安全客户端进程 处于正常运行状态,并开启实时告警,有异常登录时,及时反馈到您。
及时修复云服务器系统组件与 Web 组件存在的安全漏洞。
说明
做好如上云服务器系统安全防护,虽可有效降低安全风险,但也无法保证绝对安全,建议定期做好云服务器系统的安全巡检及数据备份,以防突发情况导致数据丢失、或业务不可用。
常见问题
是否支持关闭异常登录检测?
不支持关闭异常登录检测。
如果您不想接收异常登录的告警通知,您可以尽量配全登录白名单,或者关闭异常登录告警。
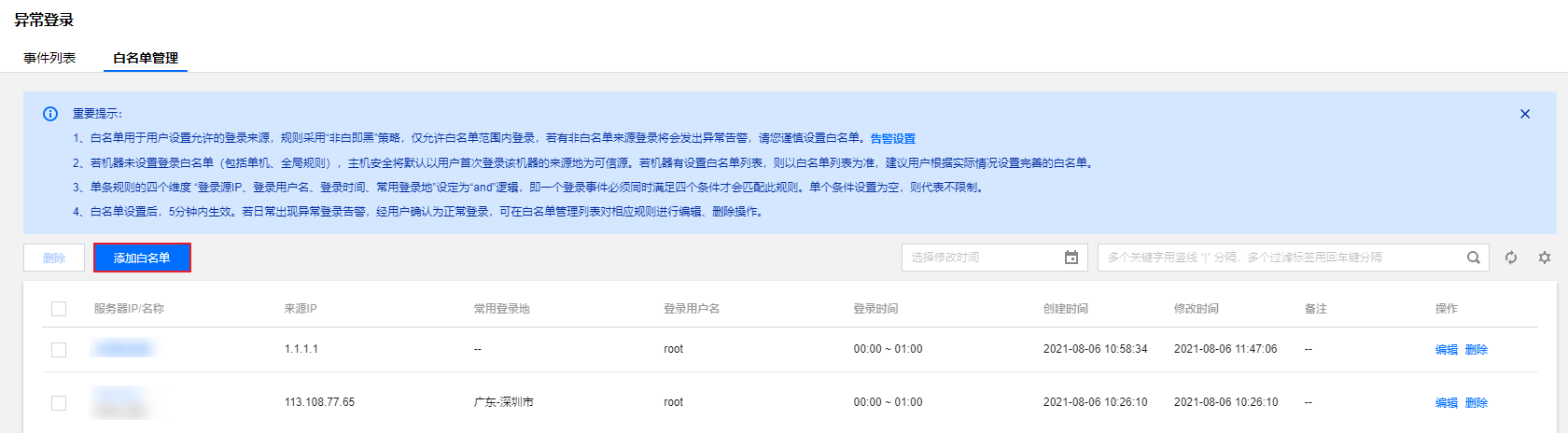
配全登录白名单:在 异常登录页,选择白名单管理 > 添加白名单,将常用登录来源 IP 添加为白名单。
关闭异常登录告警:在 告警设置页面,将告警状态设为关闭,或取消勾选告警项“高危”或“可疑”即可。

文档反馈