恶意请求
Download
聚焦模式
字号
本文档将为您介绍如何查看并操作恶意请求告警列表及策略配置。
背景信息
恶意请求功能提供对外界请求行为进行实时监控及处理的能力,有效识别恶意请求行为。若主机向恶意域名发起请求会被识别并记录,检测到此类恶意请求行为,系统会为您提供实时告警。
限制说明
恶意请求监测支持专业版、旗舰版主机。
恶意请求拦截仅支持 Linux 系统的旗舰版主机,且仅支持拦截服务器做 DNS 查询,不支持拦截流量上的转发。
告警列表
1. 登录 主机安全控制台,在左侧导航栏,选择入侵检测 > 恶意请求。
2. 在恶意请求页面,可查看恶意请求告警列表,并进行相关操作。

筛选:支持按命中策略类型、状态、最近请求时间、状态及关键字进行筛选。
自定义展示列:单击

导出:单击

字段说明:
主机名称/实例 ID:对恶意域名发起请求的主机名称及实例 ID
IP 地址:对恶意域名发起请求的主机IP
命中策略类型:
系统策略:系统策略为腾讯主机安全运营专家与算法专家经过多模型沉淀的规则配置,适用于大部分的恶意请求检测。
用户自定义策略:用户根据业务情况对相关域名设置告警/拦截/放行动作。
命中策略:主机请求恶意域名所命中的策略名称。
恶意请求域名:域名或IP 地址
请求次数:主机请求次数
危害描述:请求该恶意域名可能造成的危害。
最近请求时间:最近一次请求该恶意域名的时间。
状态:待处理、已加白、已处理、已忽略、已拦截。
详情:可查看该恶意请求事件的详细情况,含风险主机信息、恶意请求详情、危险描述、修复建议。


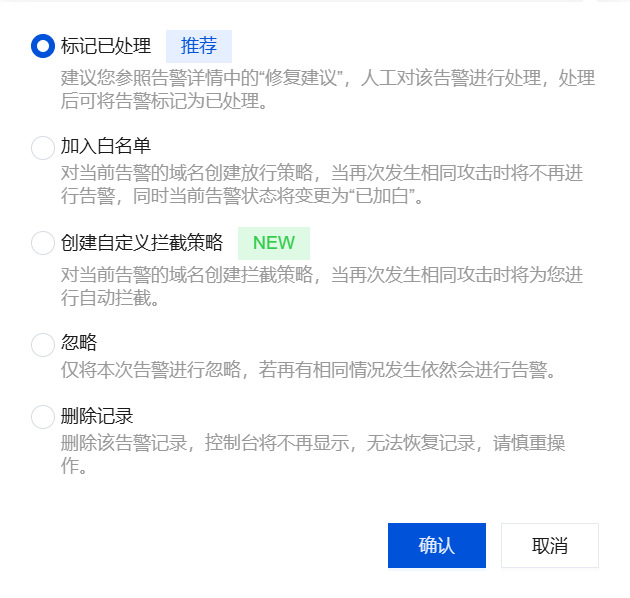
处理:标记已处理、加入白名单、创建自定义拦截策略、忽略、删除记录。
策略配置
管理策略

筛选:支持按策略类型、执行动作、生效状态、关键字进行筛选。
自定义展示列:单击

导出:单击

字段说明:
策略名称:系统策略固定名称,分别为:系统规则(重保)、系统规则(标准);用户自定义策略则为用户所设置的策略名称。
策略类型:系统策略、用户自定义策略。
黑/白名单:该策略属于白名单/黑名单。
域名详情:IP/域名或泛域名。
生效主机:该策略生效的主机范围。
更新时间:最近一次更新策略的时间。
执行动作:请求访问域名时命中策略将自动执行的动作(放行/告警/拦截)。
生效状态:策略是否生效。
编辑:对策略进行编辑。
删除:删除该策略。
创建策略:
黑名单:当主机请求了黑名单中的域名,将执行告警/拦截动作。
白名单:当主机请求了白名单中的域名,将执行放行动作。


注意:
系统策略是内置策略,不支持新增、编辑和删除,仅支持开关。
系统策略(标准)建议保持开启状态,系统策略(重保)建议在重保期间按需开启。
用户自定义策略中,拦截策略仅对旗舰版主机生效。
系统自动拦截规则
恶意请求功能新增系统自动拦截规则,开启后,支持自动拦截检测出的系统黑域名和黑 IP,部分内容仍需您手动配置策略。
系统黑名单域名和 IP:主机安全运营专家与算法专家经过沉淀的域名和 IP 名单,此名单中的域名和 IP 可进行自动拦截。
拦截原理说明:恶意请求指的是终止对规则域名/IP的访问过程,它不会结束进程,而是会终止该访问请求。
1. 登录 主机安全控制台,在左侧导航栏选择入侵检测 > 恶意请求。
2. 在恶意请求页面,支持如下两种方式开启系统自动拦截规则。
在策略配置页面,单击系统自动拦截规则策略右侧的生效状态开关。

在告警列表页面,单击开启恶意请求自动拦截开关。

文档反馈