云防火墙与其他产品的联合防护
Download
聚焦模式
字号
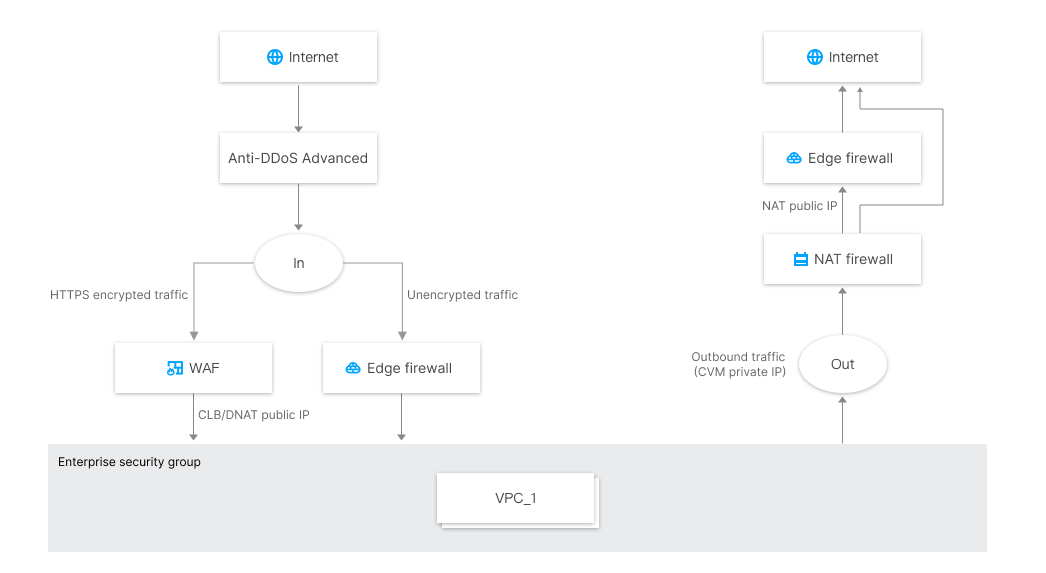
对于入方向流量
云防火墙和 WAF 共同组成了云上网络安全的整体边界防护,WAF 更偏向于对加密的 HTTPS 流量进行防护,非加密流量通过云防火墙集成的威胁情报、 入侵防御系统(IPS)的基础规则和虚拟补丁等进行安全防护。
SaaS 化 WAF 和互联网边界防火墙是并行工作,流量经过 SaaS 化 WAF 后,不再经过互联网边界云防火墙,但流量可回源到 NAT 边界 FW 的 DNAT IP。
CLB 类型 WAF 和云防火墙是串联部署,流量先经过互联网边界防火墙,再经过 CLB WAF。
使用腾讯云 CDN 回源到 CLB、CVM 的流量仍然会经过互联网边界 FW。
对于出方向流量
可以通过 NAT 边界 FW(防火墙),实现基于云服务器(CVM)颗粒度的主动外联控制,并且支持基于域名的访问控制,结合腾讯威胁情报,可对主动外联的恶意 IP 及域名进行自动拦截。
如未开启 NAT 边界 FW,则只能在互联网边界 FW,对 NAT gateway 后的流量进行访问控制,此时云防火墙看到的是公网 IP。
云防火墙和安全组是两个独立的系统,策略同时放通,流量才放行。
在云防火墙企业版中,集成了企业级安全组功能,可以通过企业级安全组,灵活的实现 VPC 间、同 VPC 子网间及 IDC 专线间的访问控制和阻挡日志。
说明:
云防火墙产品支持基于公网 IP 地址颗粒度的防护,因此您可以根据企业自身的情况选择开启方式:
只开启部分资产的防护以节省费用。如果企业预算允许,我们仍然建议您开启云上全部资产的防护,以免黑客从非重要资产入侵。
如果您云上资产只对外暴露了 Web 类业务,且已经被 WAF 防护,可以只开启主动外联的防护,形成从外到内的 WAF 防护,从内到外的云防火墙防护的整体网络安全防护方案,以节省您的宝贵投资。
云防火墙产品具备几十 Gbps 大带宽流量的游戏、电商行业大型客户应用案例,当您的业务流量超过1Gbps时,您可以联系您的商务经理,沟通定制商务方案。
文档反馈