概览
Download
聚焦模式
字号
功能简介
规则引擎旨在通过丰富的规则语言,满足更加灵活、细粒度的业务需求。您可按需自定义匹配类型,并应用于对应的操作。相较于站点加速侧的配置,规则引擎的优先级更高,即在规则引擎创建的自定义策略将覆盖站点加速的配置。
适用场景
站点加速侧的站点级配置无法覆盖全部业务需求,不同子域名,路径或文件后缀等匹配条件下存在差异化配置。
当前业务除了需要缓存,HTTPS 等基础配置,还需要自定义 Cache Key, URL 重写和修改 HTTP 头部等其他加速功能。
关键术语
定义 | 说明 |
规则 | 包含特定类型的请求以及应用于它们的一系列操作。 |
条件表达式 | 定义识别请求的逻辑,支持以下类别: IF注1 ELSE IF ELSE |
匹配条件 | 定义识别请求的标准,包括: 匹配类型 运算符 值 |
And/Or | 逻辑与/逻辑或,可连接多个匹配条件。 |
操作 | 命中的请求执行的一系列功能配置。 |
说明:
注1:
IF 语句可以嵌套在一层 IF 语句下,即执行内嵌 IF 语句之前必须先满足最外层 IF 语句。规则生效优先级
范围 | 说明 |
站点加速 vs 规则引擎 | 若站点加速与规则引擎配置了同一个操作,则规则引擎优先级更高,为最终生效的配置。 |
规则引擎的单条规则内 | 如果 IF 语句内存在嵌套的 IF 条件,执行内嵌 IF 语句必须先满足最外层 IF 条件。 如果存在多个同级的 IF 条件,按 IF 条件的相对顺序,从上至下执行,即如果同时匹配到多条规则,下方规则的操作将覆盖上方的规则。 如果同时存在 IF、Else IF、Else,则满足其中任意一个 IF、Else IF 条件时,执行对应操作后结束,不会再继续匹配当前 IF 条件下的其它规则,如果都不满足,则按照 Else 规则内操作执行。 |
规则引擎内的多条规则 | 按相对顺序,从上至下执行。 提示:确定规则放置位置时,可将具有通用性或粗粒度的规则放在上方位置作为默认配置,针对特定请求或细粒度的规则放在下方位置。 |
注意:
有两种场景的执行较为特殊:
无论 Token 鉴权 不管出现在哪个位置,它始终是最先执行的。例如,如果一个请求同时命中了两条规则,即使 Token 鉴权操作在下方的规则中,它也会最先执行,鉴权通过才继续执行剩下的内容。
对于包含跳转逻辑的操作,如访问 URL 重定向和强制 HTTPS,它们的执行方式为 Break。这意味着,如果同一个请求命中了跳转操作和其他操作,那么在执行跳转操作后,将不再继续执行下方其他操作。
规则生效优先级示例
示例一:IF 条件内嵌套 IF 匹配
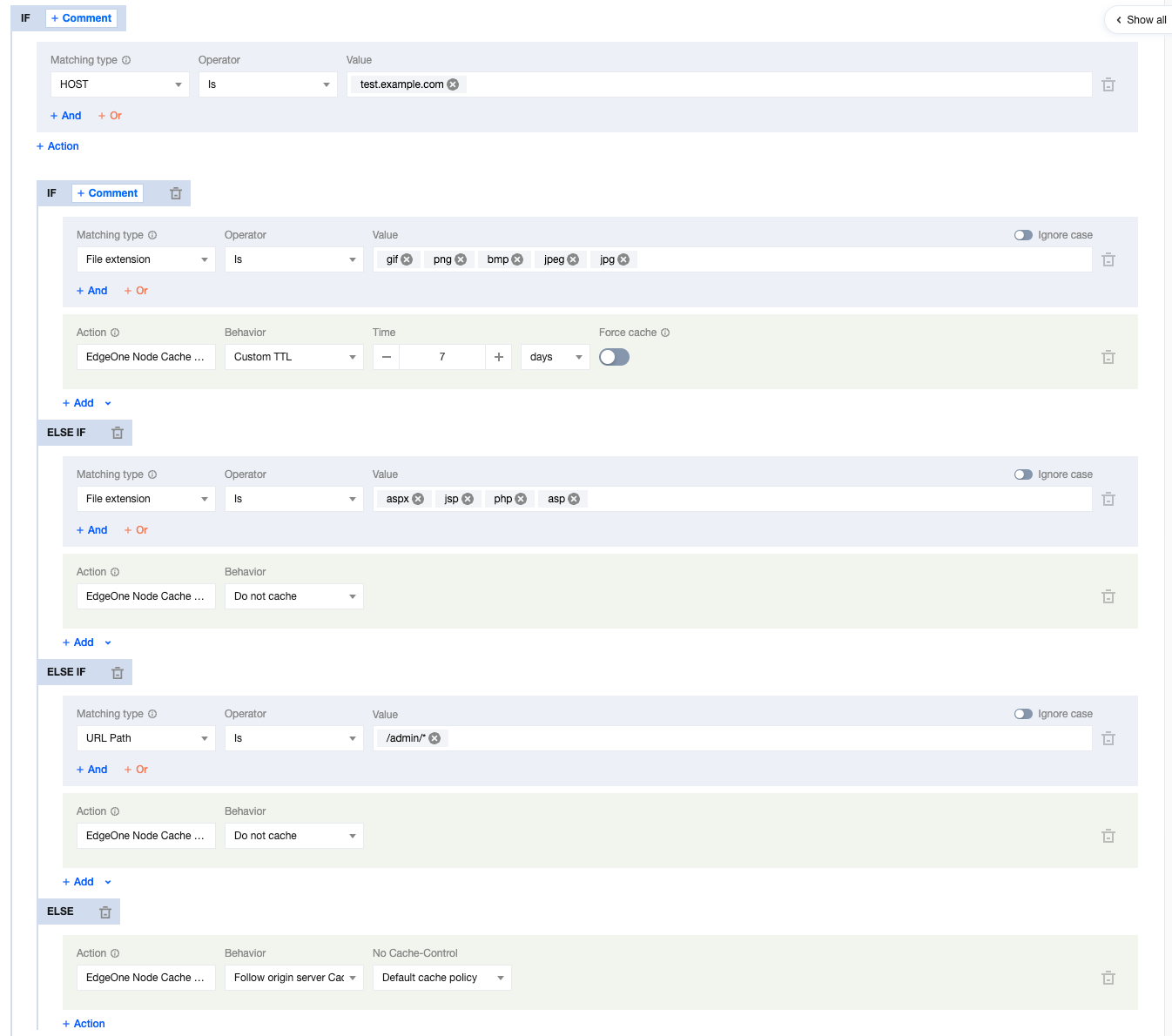
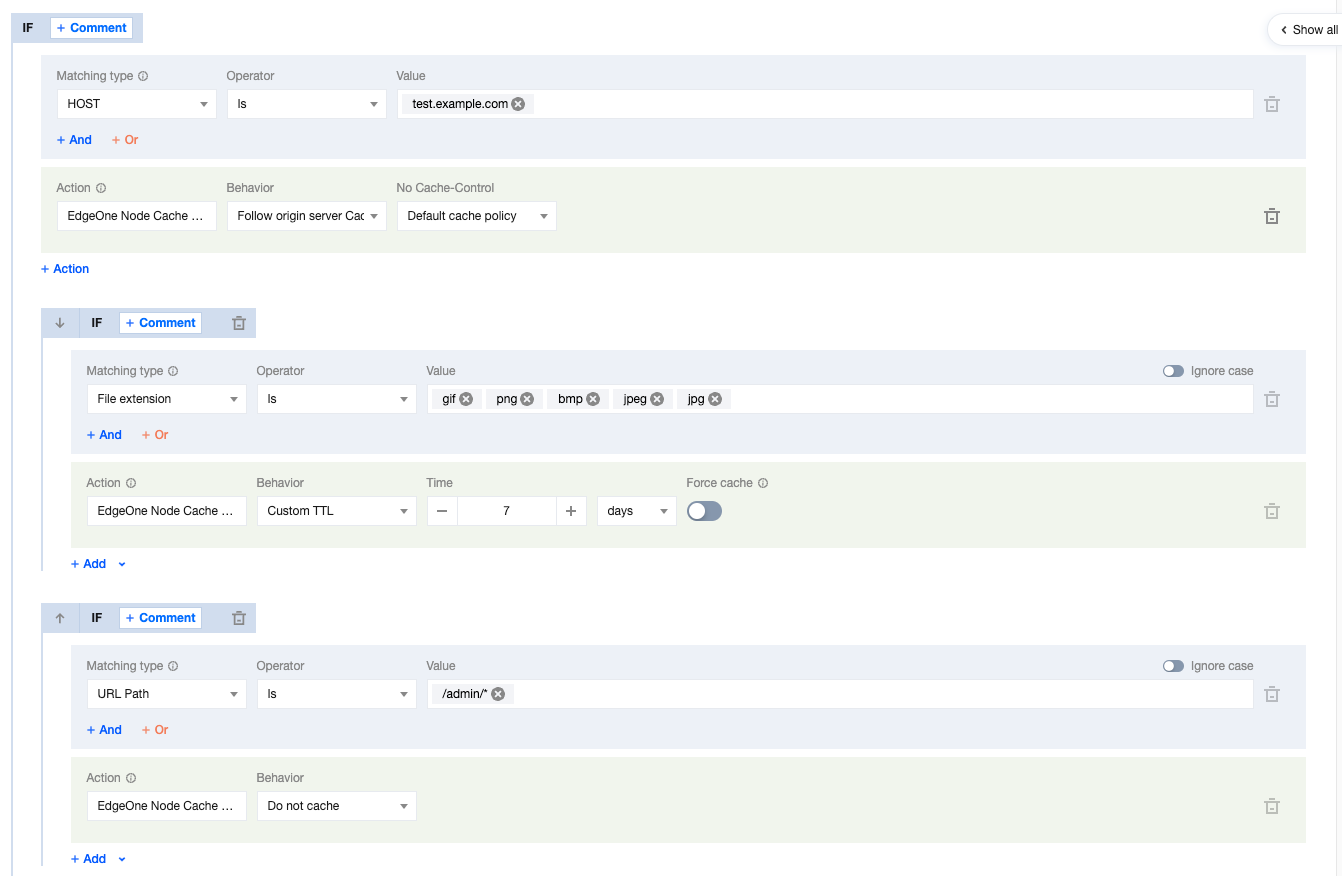
当前用户的节点缓存 TTL 规则配置如下所示,存在多层嵌套 IF 条件。
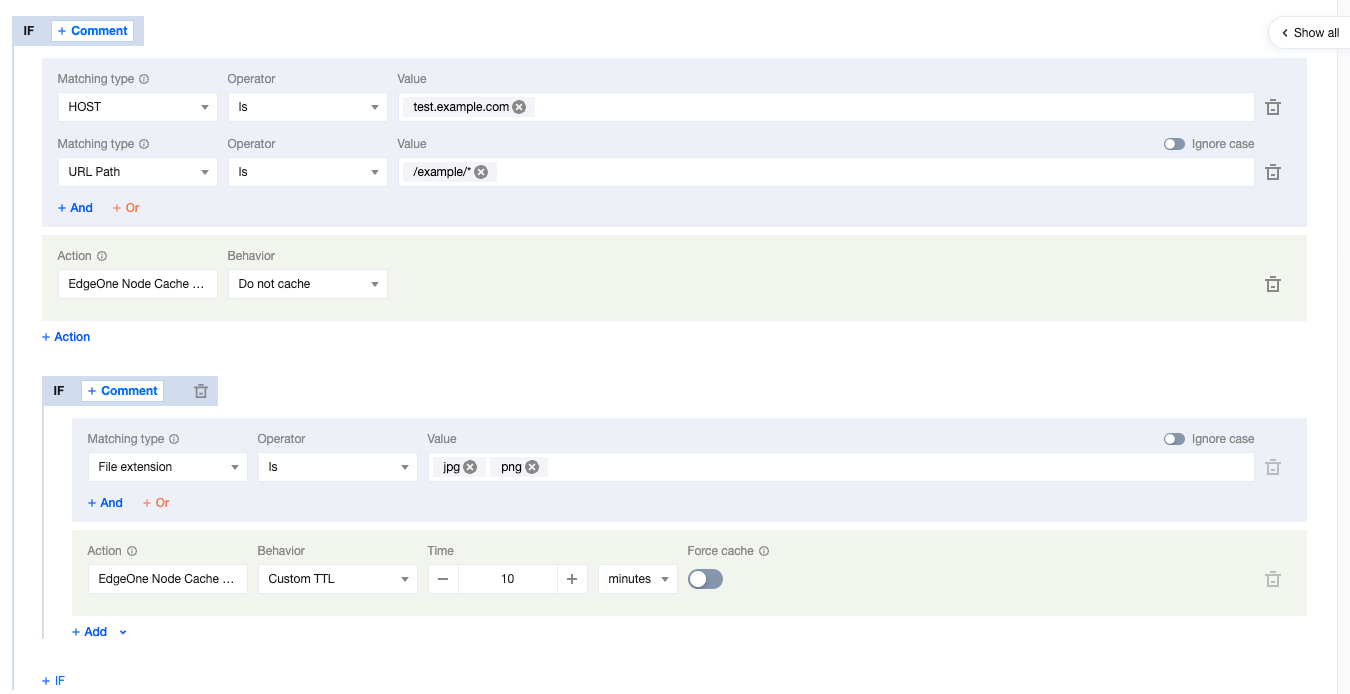
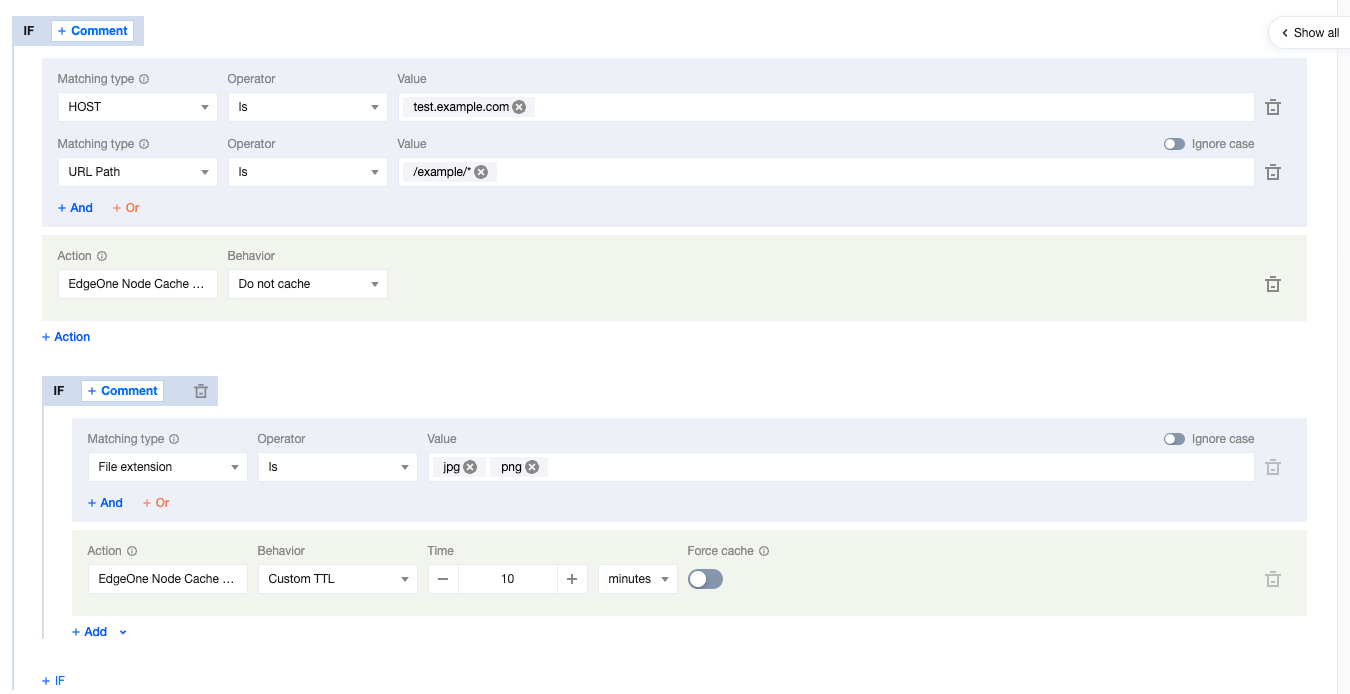
则用户请求的 URL 缓存行为按照如下行为生效:
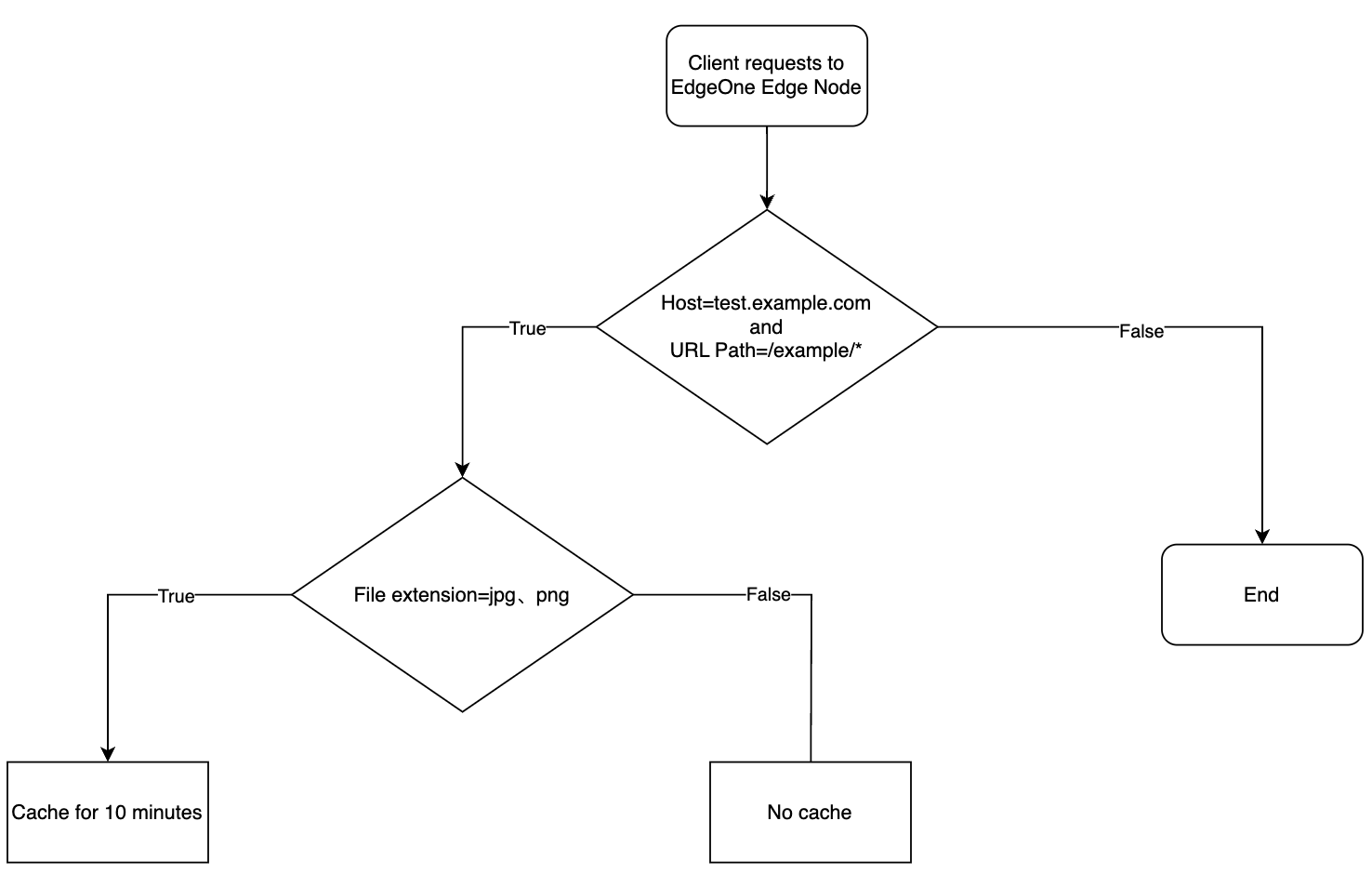
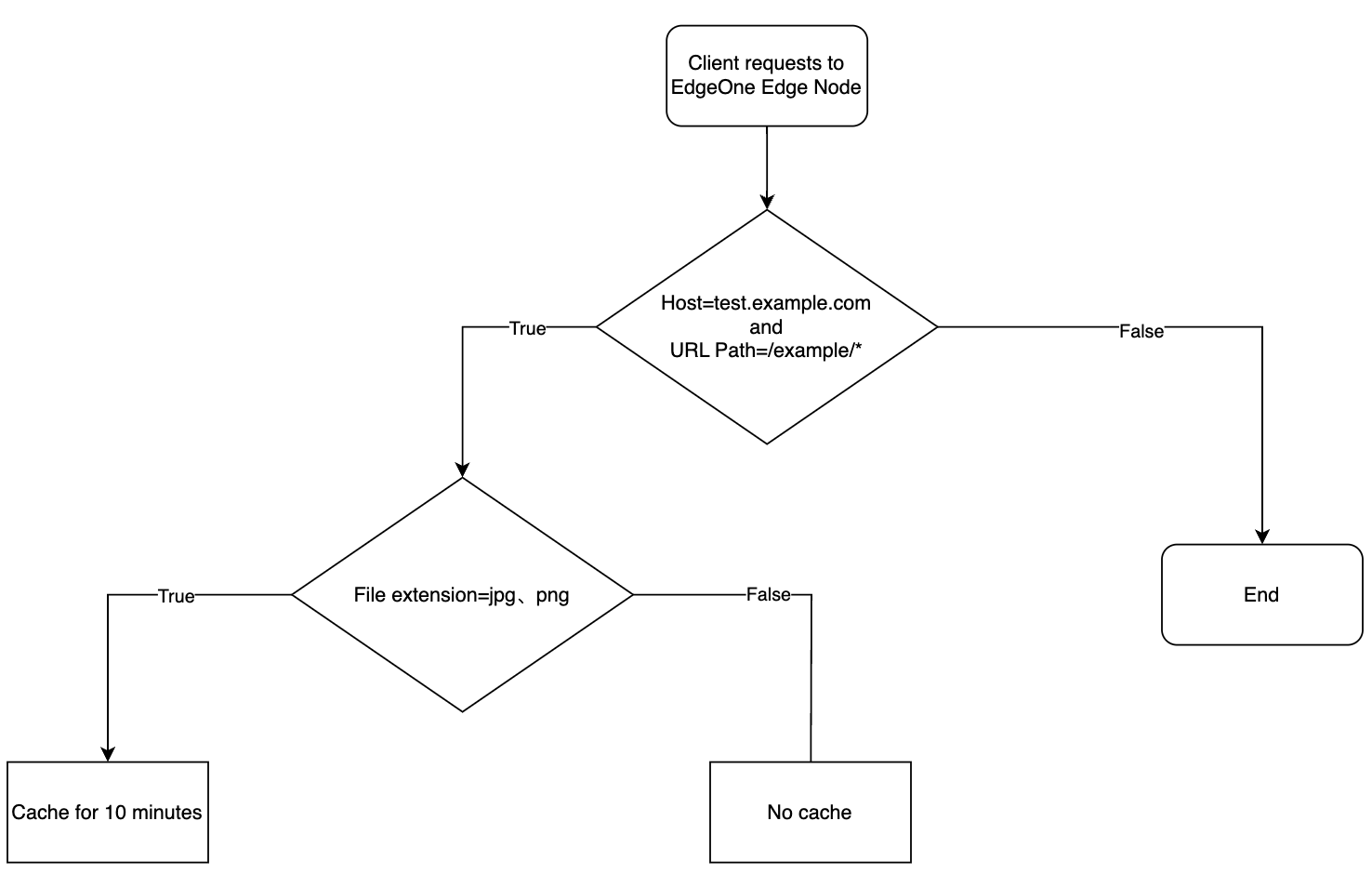
当请求 URL 为:
https://test.example.com/example/1.jpg时,文件缓存10分钟。当请求 URL 为:
https://test.example.com/example/1.mp4 时,文件不缓存。当请求 URL 为:
https://test.exampel.com/vidoe/1.jpg 时,不会匹配到该规则。示例二:IF 条件内包含多个同级 Else IF 匹配
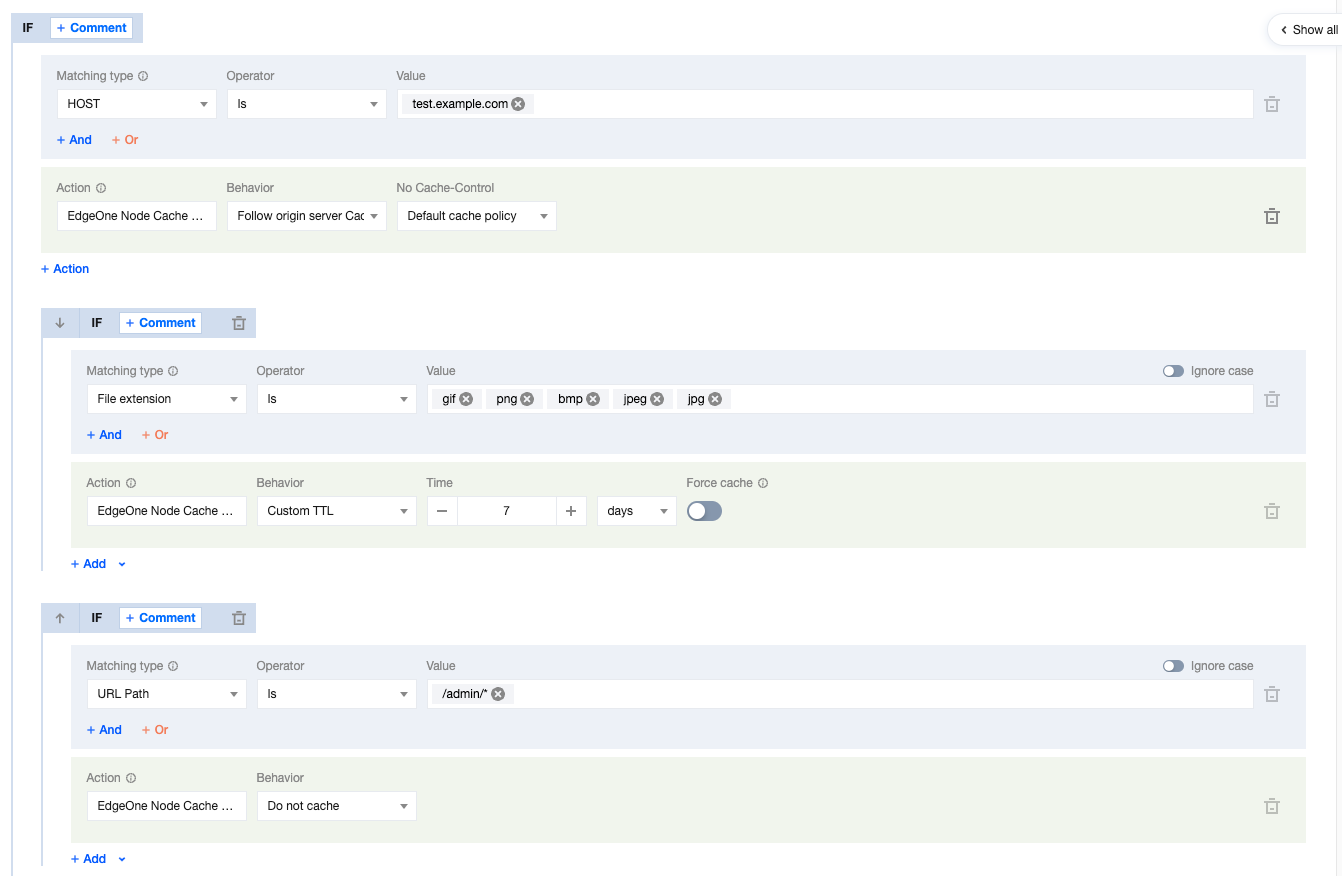
当前用户的节点缓存 TTL 规则配置如下所示,存在多个同级 Else IF 条件。
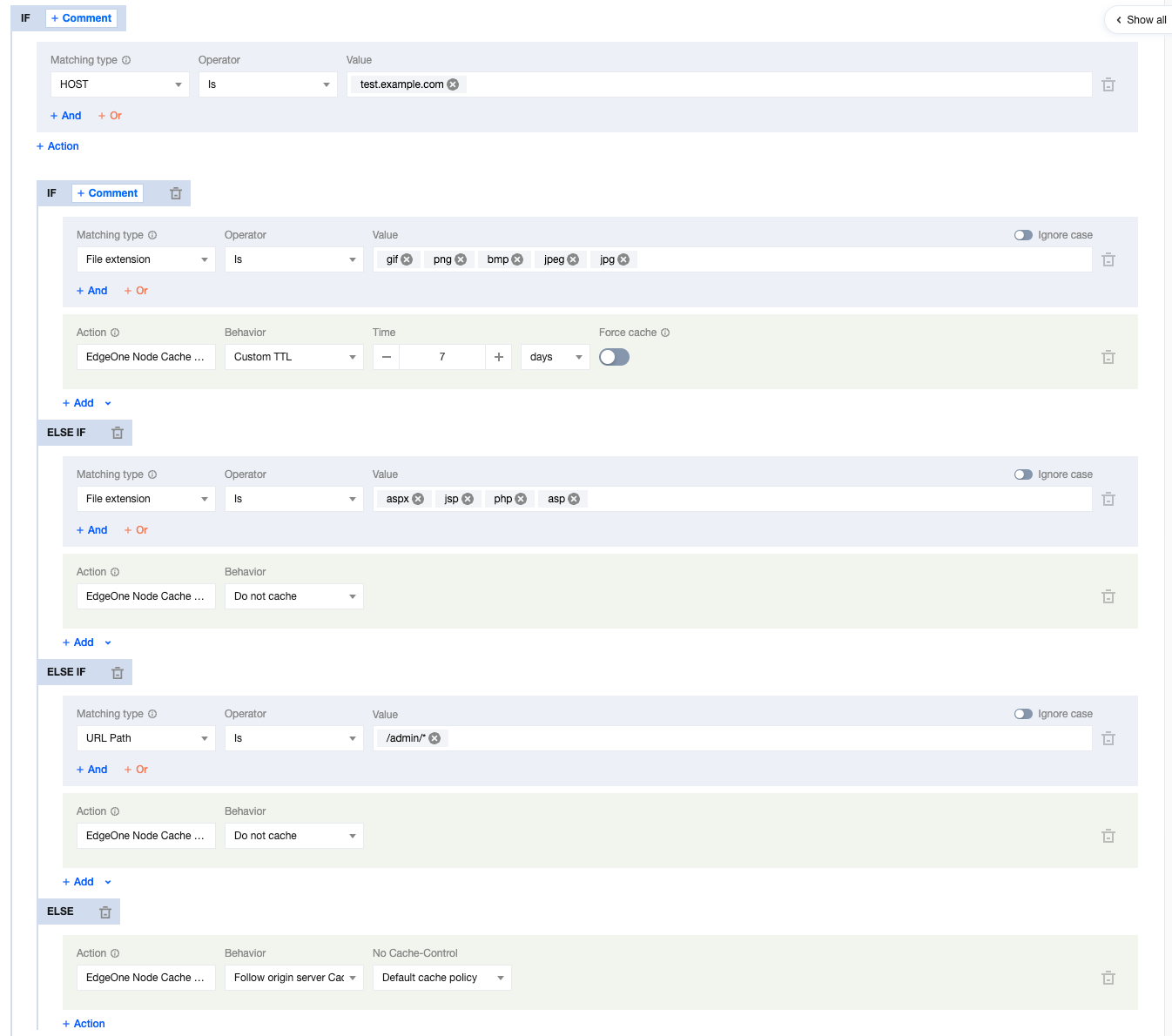
则用户请求的 URL 缓存行为按照如下行为生效:
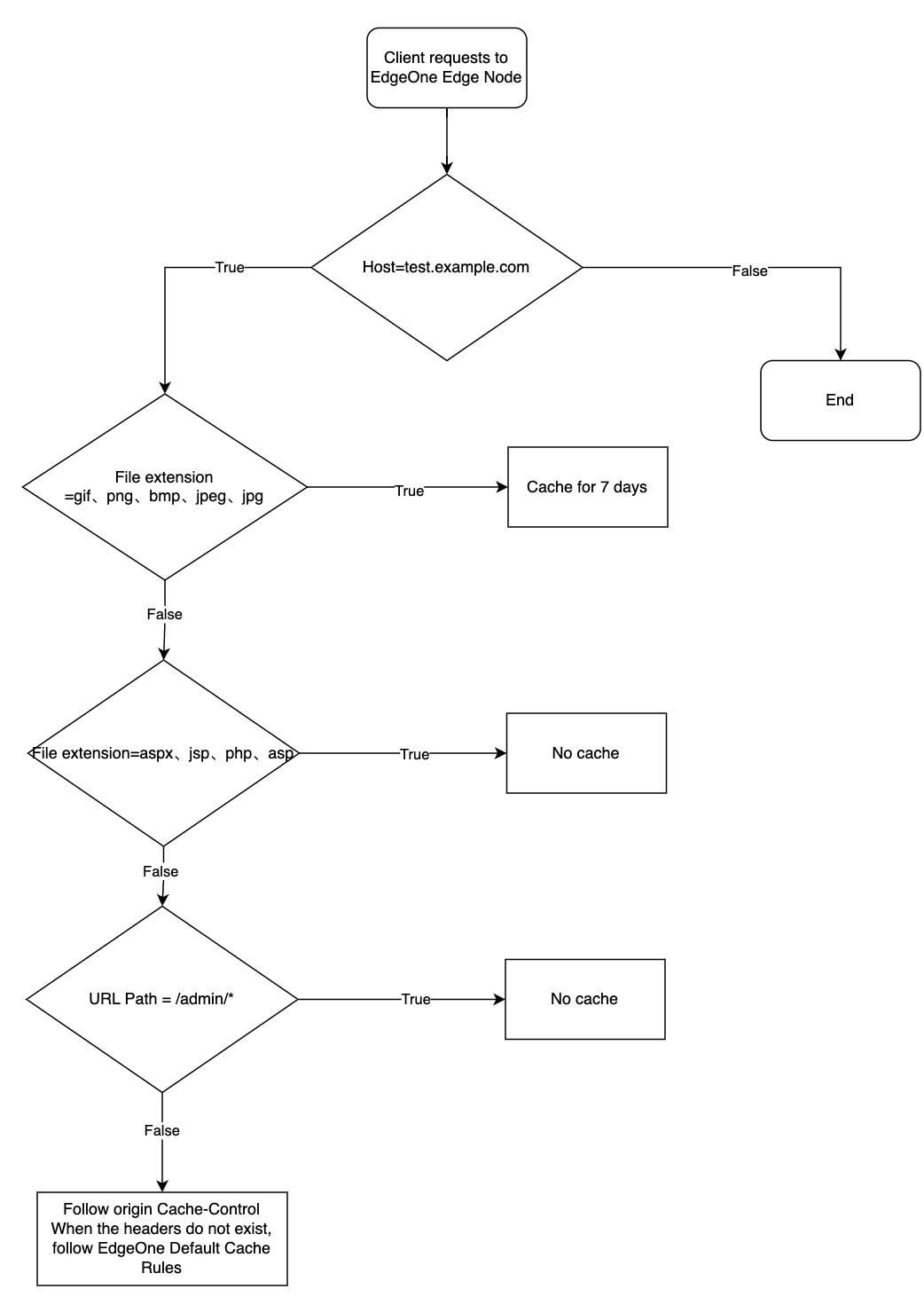
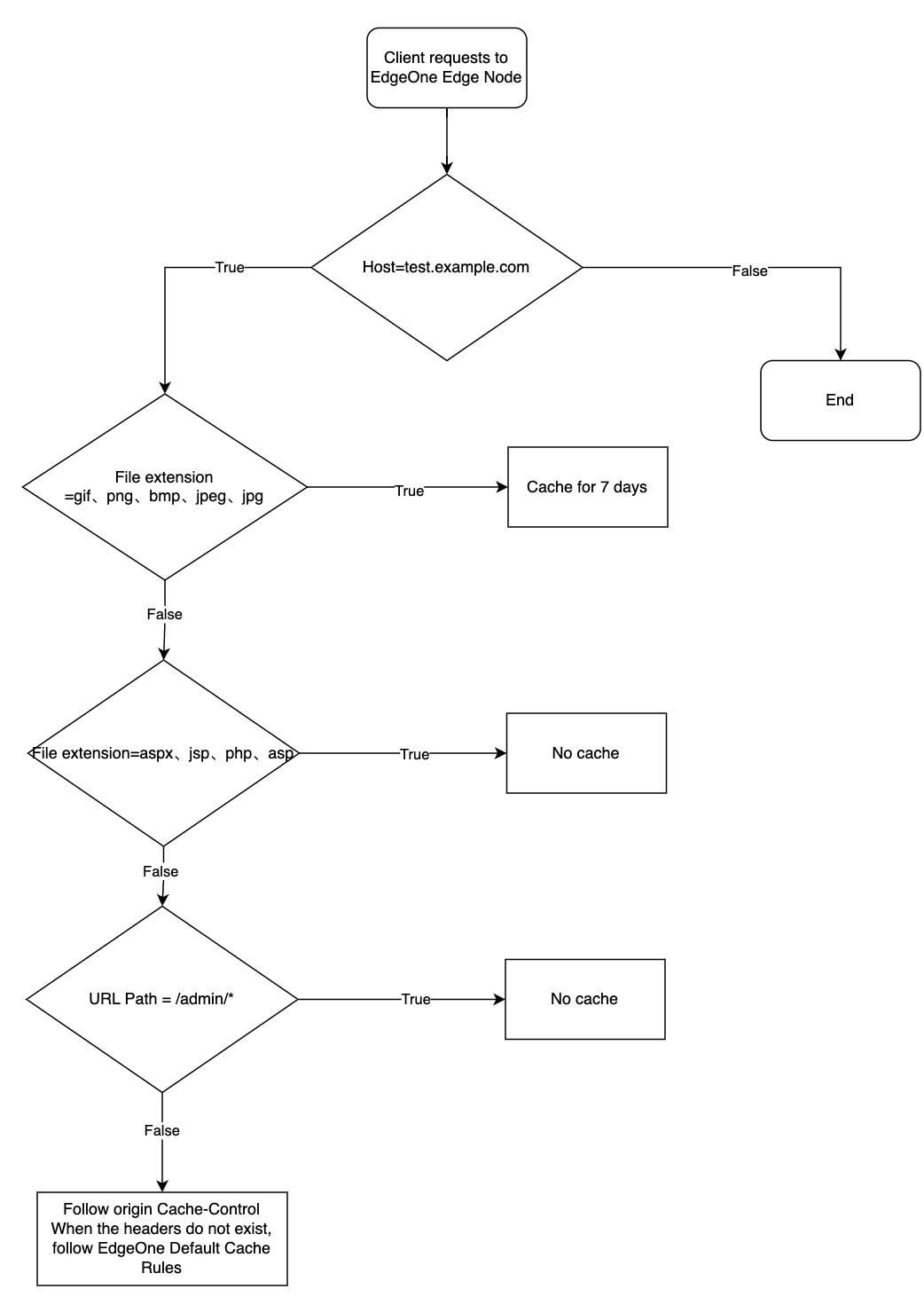
当请求 URL 为:
https://test.example.com/image/1.jpg 时,文件缓存7天。当请求 URL 为:
https://test.example.com/index/1.jsp 时,文件不缓存。当请求 URL 为:
https://test.exampel.com/admin/1.php 时,不缓存。示例三:多个同级 IF 条件匹配
当前用户的节点缓存 TTL 规则配置如下所示,存在多个同级 IF 条件,则连续的 IF 条件,下方条件的生效优先级顺序最高。
则用户请求的 URL 缓存行为按照如下行为生效:
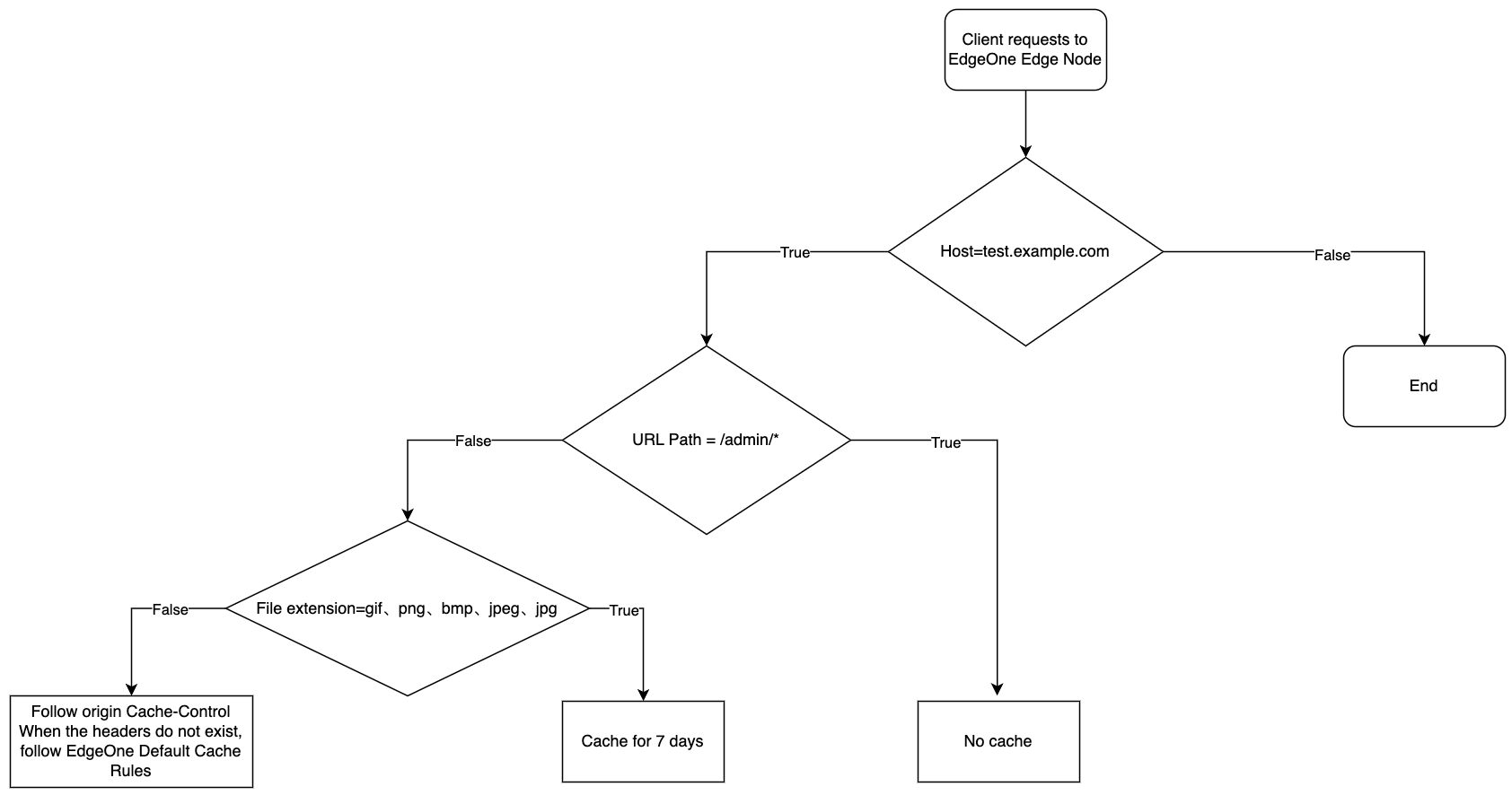
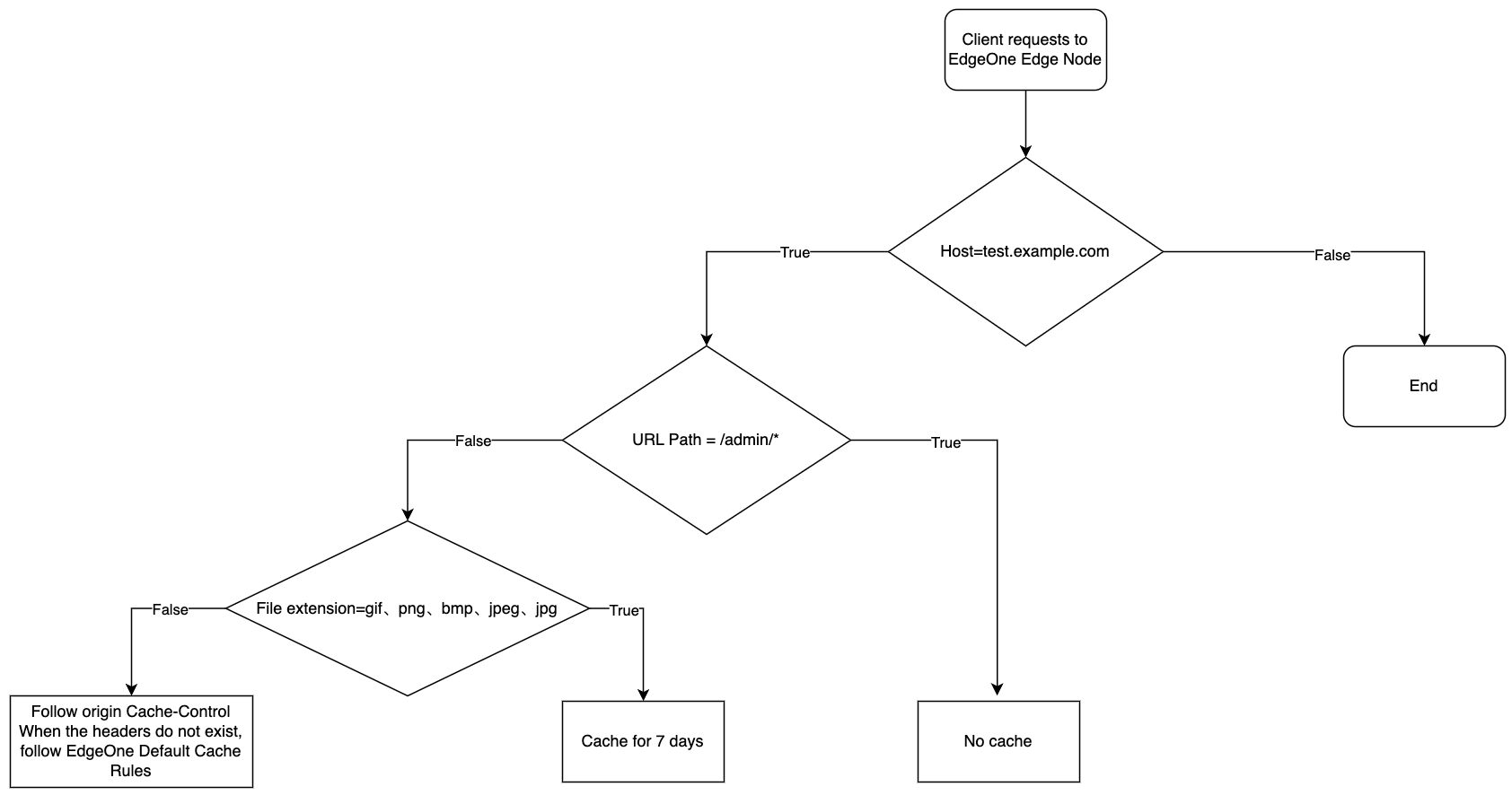
当请求 URL 为:
https://test.example.com/image/1.jpg 时,文件缓存7天。当请求 URL 为:
https://test.example.com/admin/1.php 时,文件不缓存。当请求 URL 为:
https://test.exampel.com/admin/1.jpg 时,文件不缓存。当请求 URL 为:
https://test.exampel.com/index/1.txt 时,文件遵循源站 Cache-Control 头部设置,不存在该头部时,遵循 EdgeOne 默认缓存策略。
文档反馈